Exporting IDS Rules & IOCs Export to AWS Network Firewall¶
In this guide we will manually run the AWS Export in IDSTower AWS Connector to verify that everything if working as expected and the data is indeed exported to the configured AWS Regions.
Running the export for the first time¶
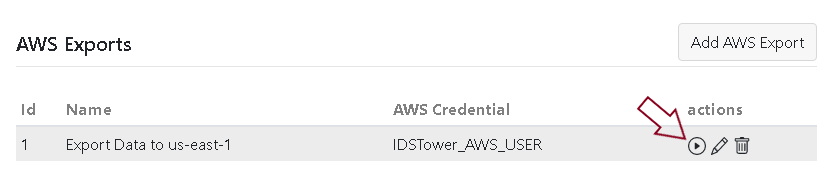
In the AWS Connector tab, click on the run button on the right of the export.
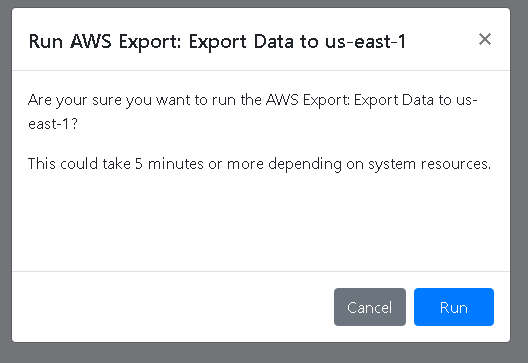
a popup screen will ask you to confirm if you want to run the export, click “Run” button to confirm.
Once you click the run button, IDSTower will start exporting the Enabled IDS Rules and IOCs from IDSTower to AWS, if any IDS Rule has an issue, we will get an error message describing the issue, disabling/updating the incompatible rules will be sufficient to solve the issue.
Note
AWS Network Firewall dose not support the full features of Suricata IDS rules language, so it is normal to find incompatible rules in your first run, especially if you are using community provided rules like Emerging Threats Open Ruleset that are created for standard Suricata setup, to learn more: Limitations and caveats for stateful rules in AWS Network Firewall .
Note
The AWS Connector will try its best to remove incompatible rules before attempting to export to AWS, this is to make sure that rules sync wont fail, if any incompatibilities/limitations are found, The AWS will display warnings.
Warning(s) means that the export were completed but some of the Rules/IOCs were removed because of incompatibilities or size limitations, AWS Network Firewall limits the stateful rule groups size to 2MB.
Once the export run is finished, you will see that the Rules & IOCs were exported to AWS successfully as seen below in one of the configured AWS Regions:
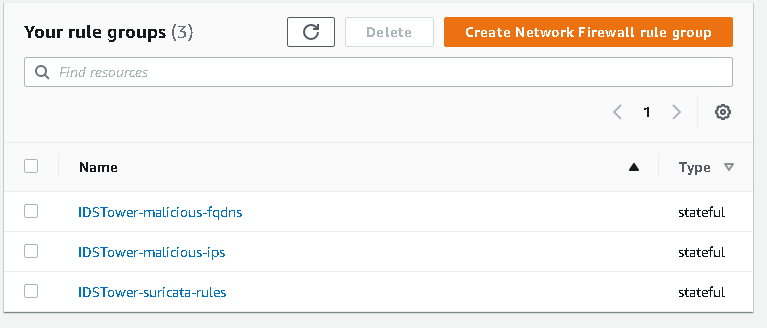
Done, from now on, IDSTower will automatically run this export every 15 minutes and will reflect any changes in IDSTower to your AWS Regions.
You can proceed now and use the above stateful rule groups created by IDSTower in your AWS Network Firewall Policies, Please follow the following AWS documentation for detailed steps: Create a firewall policy